Better Supply Chain Management: Keep Your Management System Secure & Open
Michael CousinsSupply Chain Management can be a logistical nightmare. Communication with entities outside the business and even different operating units within the same organisation can prove challenging without the type of secure management system that allows organisations to have the flexibility to share their sensitive information with those who need to see it.
The Trick to Sharing Your Supply Chain Management Software With Your Supply Chain
Sharing the content of a supply chain management software with your supply chain immediately increases the benefit of having the content in the first place. Similarly, sharing it with auditors, customers, business partners, joint venture partners and so on are all great ways of multiplying the ROI from creating the BPM system.
But what about your competitors? You wouldn’t want them looking at it.
Equally, what about sharing irrelevant information? You wouldn’t for example want to share information regarding your own internal staff appraisal processes with a joint venture partner involved in say a construction project.
So the trick is not just to enable sharing of the content of the supply chain software with those you want to see it, and to ensure those you do not want to see it are unable to. It is also to partition the content in order to suit the information needs of the specific user communities.
The Benefits of a Business Process Management System Structure
A Business Process Management system by its nature enables the organisation of processes and their related content, and the presentation of these to the end user as a coherent, linked, end-user consumable set of related process information.
For instance, a Triaster customer can have one or more Process Libraries, and each Library can be consumed by one or more groups of users.
Processes in one library can be duplicated, inherited or shared in other Libraries. Via automated import routines, processes can even be re-produced in many different brands and then shared in brand-specific Process Libraries, or even in multiple languages.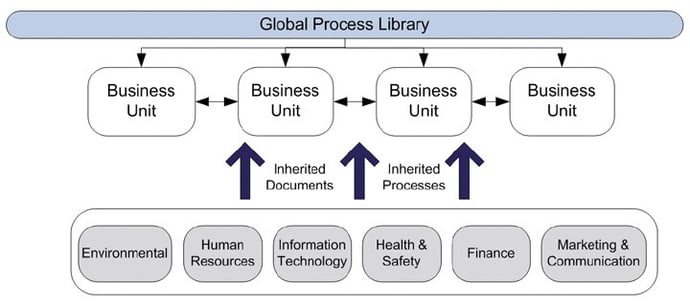
For more on creating Process Libraries that are useful and used by employees in your organisation, please 
Sharing information in a Business Process Management system with the supply chain, without compromising security and content becomes as simple as constructing a Process Library intended for the supply chain, providing it in a read-only format, and then ensuring only authorised members of the supply chain can access the Library.
For more information on BPM system structure, please read the article:
Business Process Management (BPM) system structure: Core vs Business Unit Processes
Business Process Management System Security
Most BPM systems serve their content to the end-user primarily via a HTML browser. HTML is read-only, so therefore consumers of the information cannot corrupt or change it and it can be secured using industry standard security approaches to securing a web site.
And it really is as simple as that!
The technical implementation details are not so relevant, but there are 4 main approaches depending on the specific organisational needs:
- Via Active Directory or Active Directory Federated Services for the case where only specific users that can be authenticated against a domain controller are permitted to access the content
- Via IP address where only users logging in from a specific network(s) or machine(s) can access the content – this is the typical approach for sharing a BPM system with supply chain partners when the partner has no access to the customer network
- Via user name and password where only users who have been given the user name and password can access the content – this is the typical approach for a small number of users of shared content, say the auditors or a specific business partner to whom you want to grant access
- Unsecured – open access to all users – this is the typical approach within a business where the server is hosted behind a firewall, or for those cases where the intent is genuinely for the whole world to be able to access (as in the example given below!).
Supply Chain Management Software: Process Library Designs

If you would like to look at Supply Chain Management software examples, take a look at our example Process Library - please click here to see one for yourself.
You may also find our white paper useful which explores a methodology on how to  that will actually be used in your organisation...
that will actually be used in your organisation...
Related articles:
Business Process Management (BPM) system structure: Core vs Business Unit Processes
How to share your process maps in an interactive and engaging way
How to move away from a paper based Business Process Management system
Written by Michael Cousins
Mike founded Triaster in 1994. A thought leader in business improvement, he has led Triaster ever since, spearheading its development of beautifully engineered business improvement software, that is both full of the functionality required by business analysts and that end users find really easy to use.